Is spyware for cell phones legal
Contents:
Is Mobile Spy Software Actually Legal? - Reflexintl
If you gather information, how are you going to use it? British men were the least likely, while the proportion of British women and American men who admitted to snooping were about the same. Again, British men were the most trusting, while American men and British women hovered around the middle.
On the other side of the coin, British men were most likely to confront their partner if they found such an app on their phone, although the vast majority of respondents from all groups said they would react in the same manner. Americans were slightly more likely to ask for a divorce than Brits.
Your email address will not be published.
Legal spying via the cell phone system
Save my name, email, and website in this browser for the next time I comment. This site uses Akismet to reduce spam.
- Protecting yourself.
- do i have cell spy on my phone.
- mobile spy free download windows vista sp2 64 bit;
Learn how your comment data is processed. By Paul Bischoff pabischoff Comparitech.

Stalking is a crime. You deserve to feel safe.
- Cellphone surveillance - Wikipedia.
- spy text messages iphone.
- Cell Phone Privacy Laws.
- iphone spy apps without access to phone?
In most states, police can get many kinds of cellphone data without obtaining a warrant. Law-enforcement records show, police can use initial data from a tower dump to ask for another court order for more information, including addresses, billing records and logs of calls, texts and locations. Cellphone bugs can be created by disabling the ringing feature on a mobile phone, allowing a caller to call a phone to access its microphone and listen in.
- mobile spy free download windows 7 sp2 deployment tools?
- cell phone spy zone exchange.
- Smartphone spy apps: the facts - CNET.
- Using a Cell Phone Spy Software? How to Avoid Legal Repercussions - www.narcose.nl.
- Cell Phone Tracking & Monitoring Software | mSpy App.
Intentionally hiding a cell phone in a location is a bugging technique. Some hidden cellphone bugs rely on Wifi hotspots, rather than cellular data, where the tracker rootkit software periodically "wakes up" and signs into a public wifi hotspot to upload tracker data onto a public internet server. In the United States, the FBI has used "roving bugs", which entails the activation of microphones on mobile phones to enable the monitoring of conversations.
Cellphone spying software [6] is a type of cellphone bugging, tracking, and monitoring software that is surreptitiously installed on mobile phones. This software can enable conversations to be heard and recorded from phones upon which it is installed. Cellphone spying software can enable microphones on mobile phones when phones are not being used, and can be installed by mobile providers.
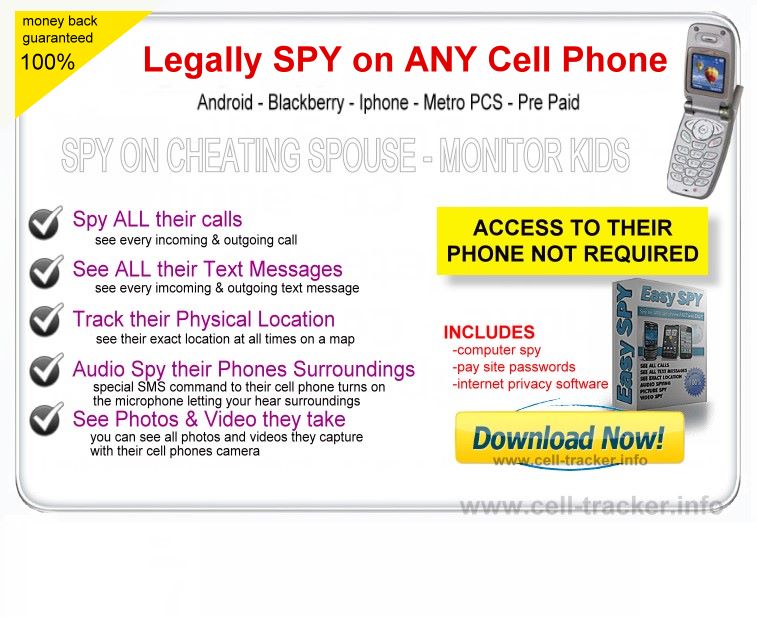
All companies selling cell phone spy software apps will have a disclaimer on You must own or have legal authority over the cell phone you wish to monitor. This is probably the most common question I am asked – “is it legal to use cell phone spy software?” As with most legal questions there is no simple answer.
In , the prime minister of Greece was advised that his, over dignitaries' and the mayor of Athens' mobile phones were bugged. Security holes within Signalling System No. Some indications of possible cellphone surveillance occurring may include a mobile phone waking up unexpectedly, using a lot of the CPU when on idle or when not in use, hearing clicking or beeping sounds when conversations are occurring and the circuit board of the phone being warm despite the phone not being used.
Spying on your kids
Preventative measures against cellphone surveillance include not losing or allowing strangers to use a mobile phone and the utilization of an access password. Another solution is cellphone with physical electric switch, or isolated electronic switch that disconnects microphone, camera without bypass, meaning switch can be operated by user only - no software can connect it back.
From Wikipedia, the free encyclopedia. Retrieved 26 March The New York Times.
Set up an account with My Spy ask about any free trials. What you need to know about Apple's critical security update". Should I be concerned? This is because that company will have full access to the person's data, messages, and private communications of any phone or Tablet you are spying on. When prompted, associate the spy app with your account.
It's not just the NSA".